In the digital age, the allure of cryptocurrency has captivated the imagination of investors, tech enthusiasts, and financial experts alike. As a revolutionary form of decentralized digital currency, cryptocurrencies promise a future where transactions are secure, transparent, and free from traditional banking constraints. However, with great promise comes great vulnerability. The very features that make cryptocurrencies attractive – anonymity, decentralization, and borderless transactions – also make them a prime target for malicious actors. This section delves into the rise of cryptocurrency and highlights its vulnerabilities, setting the stage for understanding how to protect oneself with cryptocurrency scams protection from potential scams.
The Rise of Cryptocurrency
Cryptocurrency, at its core, is a digital or virtual form of currency that uses cryptography for security. Bitcoin, introduced in 2009 by the mysterious entity Satoshi Nakamoto, was the first decentralized cryptocurrency, and since then, numerous different cryptocurrencies have been created. These are frequently called altcoins, as a blend of Bitcoin alternative.
| Year | Notable Cryptocurrencies Introduced |
|---|---|
| 2009 | Bitcoin |
| 2011 | Litecoin, Namecoin |
| 2012 | Peercoin |
| 2013 | Dogecoin, Ripple |
| 2015 | Ethereum |
| 2017 | Cardano, EOS |
| 2019 | Chainlink |
| 2021 | Polkadot, Uniswap |
The Double-Edged Sword of Decentralization
The decentralized nature of cryptocurrencies means that they are not controlled by any central authority, such as a government or financial institution. This decentralization is achieved through blockchain technology, where transactions are recorded in blocks and added to a public ledger. While this ensures transparency and security, it also means that once a transaction is added to the blockchain, it cannot be reversed. This irrevocability is what scammers exploit, knowing that once funds are transferred, they cannot be easily retrieved.
The Allure and the Vulnerabilities
The appeal of cryptocurrencies lies in their potential to offer faster, cheaper, and more secure transactions than traditional currencies. They provide financial inclusion to those without access to traditional banking systems and offer a level of privacy not available with other forms of payment. However, this very allure has also led to a surge in scams, frauds, and thefts in the crypto space. The lack of regulation, combined with the relative novelty of the technology, makes it a fertile ground for malicious actors looking to exploit unsuspecting investors.
Understanding the Landscape of Cryptocurrency Scams
The world of cryptocurrency, while brimming with potential, is also rife with risks. As the market cap of cryptocurrencies has surged, so too has the interest of scammers looking to capitalize on the uninformed and the unsuspecting. To navigate this landscape safely, it’s crucial to understand the breadth and depth of scams that have emerged over the years.
A Brief History of Notable Cryptocurrency Scams
From the early days of Bitcoin to the present, the cryptocurrency space has witnessed a series of scams that have left a trail of victims in their wake. Some scams were elaborate, involving sophisticated technology and marketing, while others were simple yet effective in their deceit.
- 2012: Bitcoin Savings and Trust was revealed to be a Ponzi scheme, with its operator, Trendon Shavers, defrauding investors of over 263,000 Bitcoins.
- 2014: Mt. Gox, once the world’s largest Bitcoin exchange, filed for bankruptcy after losing 850,000 Bitcoins, valued at over $450 million at the time, to a hack.
- 2017: BitConnect, a lending and investment platform, collapsed, leading to losses of over $1 billion. It promised high returns and operated as a classic Ponzi scheme.
- 2018: Pincoin and iFan, two ICOs run by the same Vietnamese company, scammed investors out of $660 million.
These are just a few examples, but they highlight the scale and variety of scams that have plagued the crypto community.
The Magnitude of Losses Over the Years
The financial impact of cryptocurrency scams is staggering. According to a report by CipherTrace, in the first half of 2021 alone, thefts, scams, and fraud in the crypto space amounted to $1.9 billion. This figure underscores the importance of vigilance and education in the crypto community.
| Year | Estimated Losses Due to Scams (in billions) |
|---|---|
| 2017 | $0.56 |
| 2018 | $1.7 |
| 2019 | $4.5 |
| 2020 | $1.9 |
| 2021 | $2.7 |
The Evolution of Scam Tactics
As the crypto ecosystem has evolved, so have the tactics employed by scammers. Early scams often revolved around Ponzi schemes and fake investment opportunities. Today, with the rise of DeFi (Decentralized Finance) platforms and NFTs (Non-Fungible Tokens), scammers have found new avenues to exploit. Fake DeFi projects, rug pulls, and counterfeit NFT marketplaces are becoming increasingly common.
Common Types of Cryptocurrency Scams
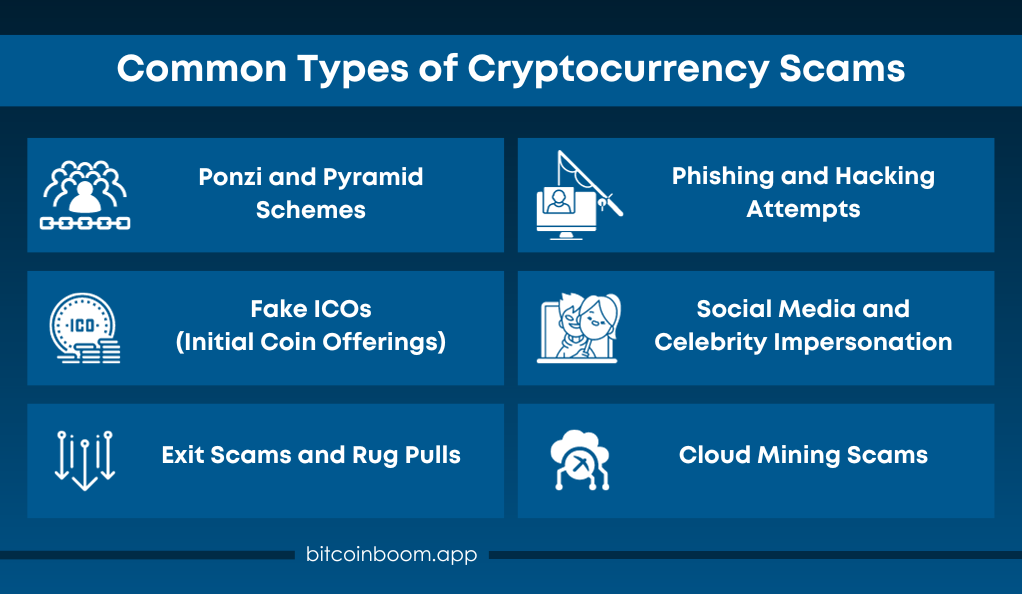
As the cryptocurrency ecosystem has expanded, so too have the methods employed by scammers. Being aware of these tactics is the first step in ensuring you don’t fall victim to them. Let’s explore some of the most prevalent types of scams in the crypto space.
- Ponzi and Pyramid Schemes
Cryptocurrency scams often mirror age-old financial frauds. Ponzi schemes promise high returns with little risk and initially use new investors’ capital to pay out returns to earlier participants. When new investments slow down, the scheme collapses. Pyramid schemes involve participants recruiting others into the scheme, with returns based on recruitment, creating an unsustainable structure leading to financial ruin for many. - Fake ICOs (Initial Coin Offerings)
Fake ICOs lure investors with enticing websites, whitepapers, and marketing campaigns. These scams convince investors to purchase tokens that have no real value or don’t exist. Once significant investments are amassed, scammers vanish, leaving investors with worthless tokens and substantial financial losses. - Exit Scams and Rug Pulls
Exit scams often associated with ICOs see developers disappear after raising funds. Rug pulls are common in DeFi projects, where developers create a liquidity pool and suddenly drain it, resulting in significant losses for participants. Both underscore the importance of due diligence in the crypto space. - Phishing and Hacking Attempts
Scammers use phishing to create fake websites or emails that mimic legitimate crypto platforms, tricking users into providing login credentials. Hacking attempts involve direct attacks on crypto exchanges or wallets to steal funds. Using reputable platforms and robust security measures is vital to protect cryptocurrency holdings. - Social Media and Celebrity Impersonation
Social media has become a breeding ground for cryptocurrency scams. Scammers impersonate celebrities or influential figures, using their profiles to promote fake giveaways or investment opportunities. Users are enticed to send cryptocurrency to a specified address, becoming victims of deception. - Cloud Mining Scams
Cloud mining promises easy returns without the need for hardware management. Common red flags include guaranteed high returns, a lack of transparency about the mining operation, and clauses mandating “reinvestment.” Researching and verifying the legitimacy of cloud mining providers is essential to safeguard your investments.
Notable Cases of Cryptocurrency Thefts
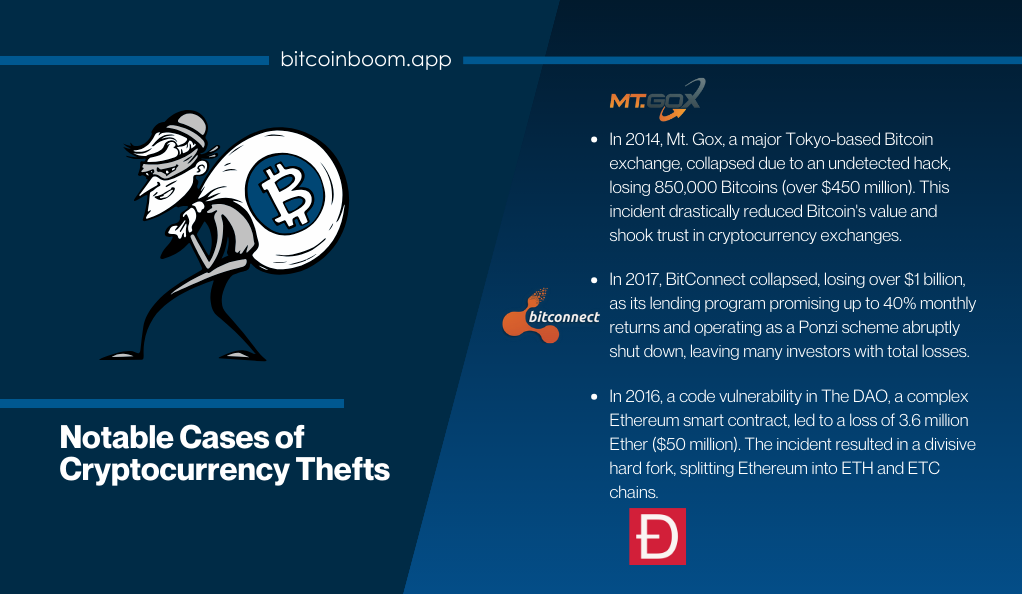
While understanding the types of scams is crucial, examining specific cases can offer deeper insights into the tactics employed by scammers and the impact on the crypto community. Here are some of the most significant cryptocurrency thefts that have shaken the industry.
The Mt. Gox Debacle
- Year: 2014
- Amount Lost: 850,000 Bitcoins (valued at over $450 million at the time)
- Brief: Mt. Gox, based in Tokyo, was once the world’s largest Bitcoin exchange. In 2014, it declared bankruptcy after a massive hack. The breach went undetected for years, allowing hackers to drain the exchange’s wallets systematically. The aftermath saw a significant drop in Bitcoin’s price and a loss of trust in crypto exchanges.
BitConnect’s Downfall
- Year: 2017
- Amount Lost: Estimated over $1 billion
- Brief: BitConnect promised high returns through a lending program. Users were encouraged to exchange Bitcoin for BitConnect tokens and were promised returns up to 40% per month. The platform operated as a Ponzi scheme, using new investments to pay returns to earlier investors. When the platform abruptly shut down, many lost their entire investments.
The DAO Hack on Ethereum
- Year: 2016
- Amount Lost: 3.6 million Ether (valued at around $50 million at the time)
- Brief: The DAO (Decentralized Autonomous Organization) was a complex smart contract on the Ethereum platform. A vulnerability in its code allowed an attacker to drain funds from the DAO. This event led to a controversial decision to hard fork Ethereum, creating two chains: Ethereum (ETH) and Ethereum Classic (ETC).
Recent Thefts and Their Impact
While the above cases are historic, the crypto space continues to witness thefts and scams. In 2020, the DeFi platform Harvest Finance was exploited, leading to a loss of $24 million. Similarly, in 2021, the Poly Network was hacked, resulting in a staggering loss of over $600 million, though the hacker later returned most of the funds.
How Scammers Operate
To protect oneself, it’s essential to understand the mindset and tactics of scammers. Here’s a glimpse into their modus operandi:
Techniques Used by Scammers
Scammers employ a variety of techniques to manipulate and deceive individuals. Social engineering is a common tactic where they manipulate people into revealing confidential information, often using psychological manipulation to gain trust. Additionally, they exploit emotions such as fear and greed, enticing victims with promises of high returns and minimal risk. Misinformation is another tool in their arsenal, as they spread false information or rumors to manipulate market sentiment and lure unsuspecting investors into their schemes.
The Role of Social Media and Celebrity Endorsements
Social media platforms have become fertile ground for scammers to reach a broad audience quickly. They create fake profiles, run deceptive ads, or even compromise legitimate accounts to spread their scams. One prevalent tactic is celebrity impersonation, where scammers pose as well-known figures to endorse fake giveaways or investment opportunities, leveraging the trust people place in celebrities.
Understanding the Psychology Behind Scam Tactics
Scammers capitalize on human emotions and cognitive biases to achieve their objectives. One such bias is confirmation bias, where individuals tend to believe information that aligns with their existing beliefs, making them susceptible to echo chambers created by scammers. Overconfidence is another vulnerability that scammers exploit, as individuals may overestimate their knowledge or abilities, leading to risky decisions.
Lastly, herd mentality often plays a role, with scammers creating an illusion of widespread endorsement or participation to lure victims into their fraudulent schemes. Understanding these psychological triggers is crucial to recognizing and guarding against scams in the crypto world.
Protecting Yourself from Scams

The dynamic world of cryptocurrency offers immense opportunities, but it also presents significant risks. As the adage goes, “Forewarned is forearmed.” By adopting best practices and staying vigilant, you can safeguard your investments and navigate the crypto landscape with confidence.
- Importance of Due Diligence
Before diving into any cryptocurrency venture, conduct thorough research. Check reviews on platforms like Trustpilot and Reddit to gain insights from others’ experiences. Verify the legitimacy of the platform or project by scrutinizing the team and their past projects. Understanding the project’s whitepaper, tokenomics, and its purpose is essential for informed decision-making. - Recognizing Red Flags and Warning Signs
Vigilance is crucial. Watch for red flags like promises of unrealistically high returns and pressure to make quick decisions. Legitimate projects are transparent about their operations. Being aware of these signs can protect your investments. - Using Secure Wallets and Exchanges
Security hinges on your choice of platforms. Hardware wallets like Ledger and Trezor are secure options for storing significant holdings. Reputable exchanges with 2FA and cold storage options add an extra layer of protection. - The Role of Two-Factor Authentication (2FA) and Other Security Measures
Enable 2FA, but avoid SMS-based methods due to vulnerabilities. Instead, use authenticator apps like Google Authenticator. Keep software updated for security patches and stay vigilant against phishing attempts by double-checking URLs and bookmarking trusted sites. These measures, rooted in due diligence and security awareness, offer robust protection against crypto scams.
Legal and Regulatory Measures Against Scams
Governments and regulatory bodies worldwide are becoming increasingly proactive in combating crypto scams.
Actions Taken by Governments and Regulatory Bodies
- Regulations: Many countries are introducing regulations to govern ICOs, exchanges, and other crypto-related activities. This provides a framework for legitimate operations and a means to prosecute scammers.
- Public Awareness Campaigns: Authorities often run campaigns to educate the public about potential scams and how to avoid them.
The Role of the SEC and Other International Organizations
Organizations like the U.S. Securities and Exchange Commission (SEC) play a pivotal role in regulating and taking action against fraudulent crypto activities.
- Guidelines and Warnings: The SEC regularly issues guidelines and warnings about potential scams and what investors should look out for.
- Prosecution: The SEC and similar bodies worldwide have prosecuted numerous scammers, sending a clear message about the consequences of fraudulent activities.
Conclusion
The world of cryptocurrency is as exciting as it is challenging. While the potential for growth and innovation is vast, so too are the risks. By staying informed, being skeptical of too-good-to-be-true offers, and always prioritizing security, you can enjoy the benefits of the crypto world while minimizing its dangers. Remember, in the digital age, knowledge truly is power. Stay safe and invest wisely!





